
The Institutional Trust Architecture Blueprint
A Standard for the New Industrial Operating Layer
Addressing the 25% Trust Tax by moving from manual, retrospective audits to a real-time, Zero-Delay System State.
Author's Note: The Limits of the SiloIn my experience designing complex enterprise architectures and delivering high-stakes proofs of concept on compressed timescales, I consistently encountered the same limitation: the friction is rarely inside the building.We have highly mature enterprise solutions to optimize internal planning, reporting, and operations. Yet, the moment that data needs to cross a corporate firewall to prove compliance to a regulator, verify a claim to a partner, or validate a supply chain, the digital infrastructure completely falls apart. We revert to manual reconciliation and paper trails.I developed the Institutional Trust Architecture Blueprint to solve this exact bottleneck.This framework is not about adding another application to an already crowded enterprise stack. It is about architecting the shared, digital nervous system that sits between organizations. It is the infrastructure required to turn compliance from a retrospective audit into an automated, zero-delay system state.This is the blueprint for how we eliminate the Trust Tax and coordinate the next generation of global economic networks.— Phil TaphouseBy Phil Taphouse
[Institutional Architect/Founder]
March 2026
Contents
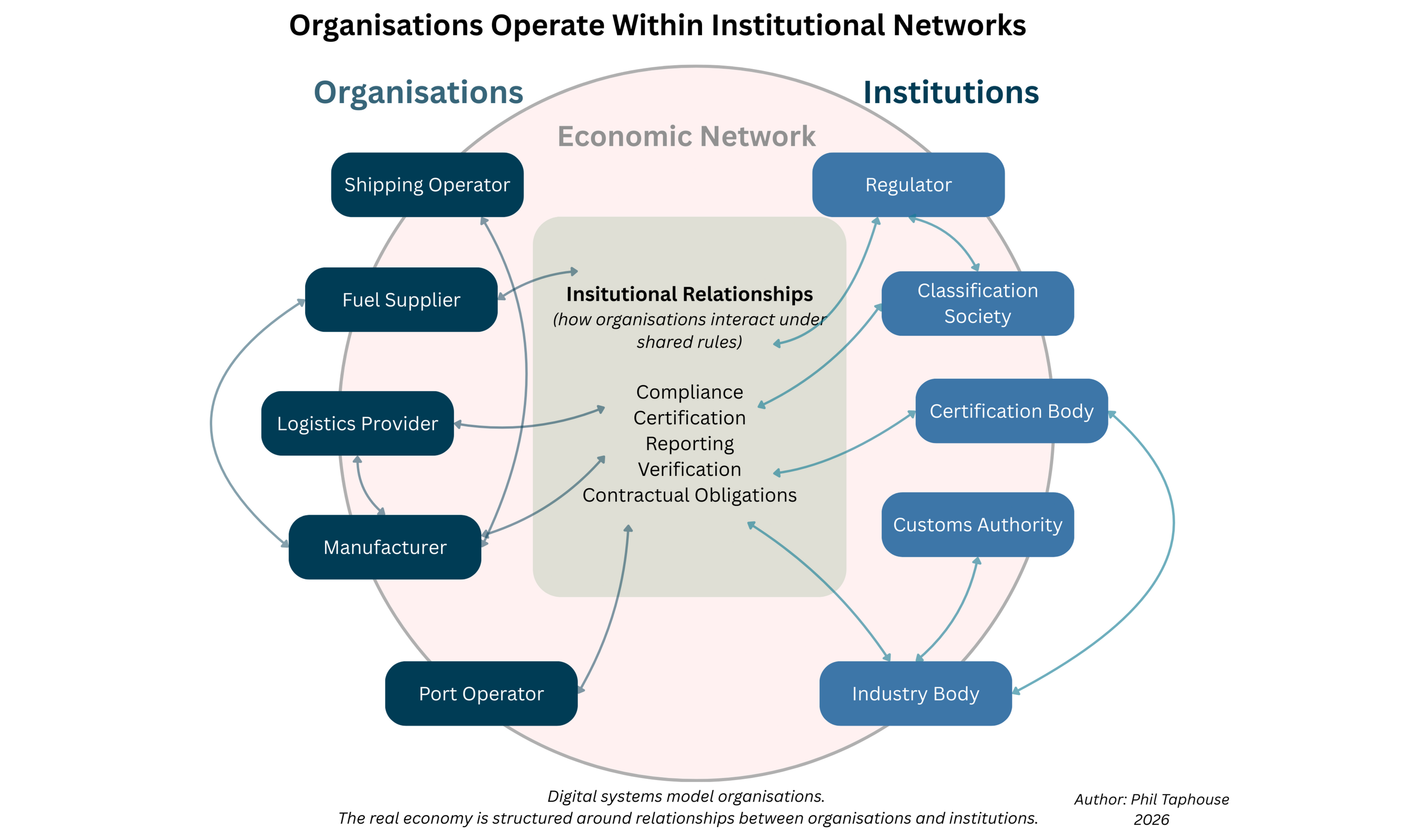
1. Core Thesis
Most digital systems today are designed to optimise activity within a single organisation. Enterprise software has become highly effective at improving internal processes — planning, reporting, operations and financial management.But organisations do not operate in isolation. Every company exists within a broader economic system — a network of regulators, suppliers, certifiers, partners, markets and institutions that collectively govern how the real economy functions.Despite this reality, our digital infrastructure stops at the boundary of the organisation.
There has never been shared infrastructure that allows participants in the real economy to interact through a common, trusted digital layer.As a result, every organisation must repeatedly recreate the same processes of trust — verifying identities, validating claims, proving compliance and establishing authority — again and again with every counterparty it interacts with.Enterprise systems optimise the company, but the economy operates across networks of institutions.
This gap is becoming increasingly visible. The enterprise software market is mature and optimisation within organisational boundaries is producing diminishing returns.Artificial Intelligence (AI) is only as good as the data it consumes, but as we move toward Agentic AI, it is only as safe as the authority it carries.In the current siloed model, AI acts on unverified data within narrow organizational boundaries. For AI to move from simple analysis to autonomous execution, it requires more than just clean data; it requires an execution boundary.Without this shared infrastructure, AI operates 'off-grid' in the white space between companies—creating an unmanaged liability instead of an industrial asset.To bridge this gap, we cannot rely on the internal tools of the last decade. For digital infrastructure to support an economy moving at machine speed, it must do more than just record transactions. It must define the exact point where policy meets action.Current enterprise systems are built to manage two states: policy (what should happen) and compliance (what did happen). What the real economy lacks today is a shared layer that governs what can happen across an entire ecosystem.What is missing is infrastructure that models the real economic network itself.The internet solved a similar problem for computers. It created a shared communication layer that allowed independent machines and networks to interact through common protocols.What the real economy lacks today is a comparable digital layer that represents how organisations, institutions and markets coordinate under shared rules.This paper introduces the Institutional Trust Architecture (ITA) — a digital infrastructure designed to coordinate identity, authority, verifiable claims and policy across institutional networks.These elements form the trust primitives of the architecture and operate independently of any single organisational platform.Together they create an institutional operating layer for the internet — infrastructure that allows organisations, regulators, certifiers and markets to interact through shared, verifiable trust mechanisms.The next generation of digital infrastructure will not simply move data between organisations — it will embed identity, authority and policy directly within institutional networks.When these primitives operate within shared infrastructure, the result is a persistent and verifiable record of economic activity across entire ecosystems.Such a network would generate value far beyond the participating organisations themselves. Regulators, insurers, auditors, risk assessors, customs authorities and governments all rely on trusted representations of economic events.A shared trust infrastructure would transform how these institutions observe, verify and coordinate the real economy.In this sense, institutional trust infrastructure represents a fundamental shift in how digital systems are designed: from software that optimises individual organisations to infrastructure that enables coordination across entire economic networks.Effectively, these elements combined can be described as an institutional operating layer for the internet.
2. The Trust Dividend: Upgrading the Economic Operating Layer
| Feature | The Status Quo (Enterprise Silos) | The Future (Institutional Architecture) |
|---|---|---|
| Trust Model | "Trust but Verify" (Manual & Human) | "Verifiable by Design" (Automated & Digital) |
| Economic Friction | The Trust Tax: ~25% overhead spent on reconciliation and audits. | The Efficiency Dividend: Real-time compliance with near-zero overhead. |
| Speed of Truth | Retrospective: We find out what happened 30 days later via a PDF. | Instantaneous: Compliance is a "system state" visible in real-time. |
| Sustainability | A Cost Center: Paying consultants to verify "Green" claims. | A Premium Asset: Verifiable provenance that increases product margin. |
| AI Utility | Hallucinations: AI guesses based on fragmented, siloed data. | Execution: AI operates on a "Nervous System" of verifiable facts. |
| Agentic AI | Ungoverned Action: AI acting on unverified data with no external "guardrails." | Execution Authority: AI constrained by verifiable policy at the point of action. |
| Data Gravity | The Firewall: Value stops at the edge of the organization. | The Network: Value scales across the entire institutional ecosystem. |
3. The Economic Case
The Economic Case: Eliminating the "Trust Tax"
While we have spent three decades and billions of dollars optimizing the internal efficiency of the firm, we have ignored the massive, systemic friction that exists between them.Today’s global economy runs on a "Trust Tax"—a multi-billion dollar drag on GDP caused by the fact that our digital infrastructure stops at the company firewall.1. The Cost of Modern Friction
Currently, every transaction between independent organisations requires a manual, retrospective "look-back." We rely on PDF certificates, third-party audits, and human reconciliation to prove what happened weeks or months ago.The Resource Drain: Estimates suggest that up to 25% of operational overhead in complex industries (like shipping, energy, and trade finance) is consumed by the "reconciliation nightmare"—proving compliance to regulators, partners, and insurers.The Opportunity Cost: Capital is locked up in "waiting for verification." Whether it’s a fuel certificate, a carbon credit, or a customs clearance, the delay is a direct hit to liquidity.2. The 25% Efficiency Dividend
Institutional Trust Architecture (ITA) moves us from retrospective reporting to real-time executable policy. By embedding identity, authority, and verifiable claims into the network itself, we eliminate the need for manual "re-verification" at every step.Zero-Delay Compliance: When policy is executable, "Compliance" is no longer a department; it is a system state.Automated Trust: ITA allows a 25% "efficiency dividend" by automating the trust primitives that currently require thousands of hours of manual audit and data entry.3. Turning "Compliance" into a Premium Asset
The biggest economic shift isn't just saving money—it’s monetizing truth.
In a world moving toward Net Zero and ethical sourcing, the attributes of a product (e.g., "This fuel is 100% green hydrogen," or "This cobalt was mined ethically") are more valuable than the product itself.The Provenance Premium: Without ITA, these claims are expensive to prove and easy to forge.Market Differentiation: With ITA, these claims are verifiable, cryptographically secure, and embedded in the transaction. This allows companies to command a premium price for verifiable sustainability, transforming a "regulatory burden" into a competitive advantage.4. The AI Multiplier
We are currently building high-speed "AI brains" on top of a "low-speed paper nervous system."
AI cannot autonomously coordinate multi-party trade if it is trapped in an organizational silo. More importantly, it cannot be safely deployed without an Execution Boundary—a digital guardrail that governs what the AI is actually authorized to do across the network.ITA provides this required substrate. It allows AI to move from simply "generating text" to "executing global economic activity," ensuring that autonomous actions are constrained by verifiable policy at the point of execution.The Bottom Line: We don't have a data problem; we have a coordination problem. Transitioning to an Institutional Trust Architecture isn't just a technical upgrade—it’s an economic imperative to unlock the next $10 Trillion of global digital value.
The Economic Imperative: Efficiency as a Survival MandateThis is not merely an administrative friction; it is a direct hit to the Cost of Sales and a systemic drain on Working Capital Efficiency.As global margins tighten and markets move to machine speed, solving this 'Trust Tax' is a survival mandate—turning slow, manual compliance into a Zero-Delay System State that protects overheads, governs automation, and unlocks trapped liquidity.
4. From Enterprise Systems to Institutional Infrastructure
Digital systems coordinate activity at different scales.Traditional enterprise software is designed primarily to coordinate activities within a single organisation.
However, as digital infrastructure expands beyond organisational boundaries, new architectural layers emerge to coordinate increasingly complex systems.These layers can be understood as different scopes of coordination.
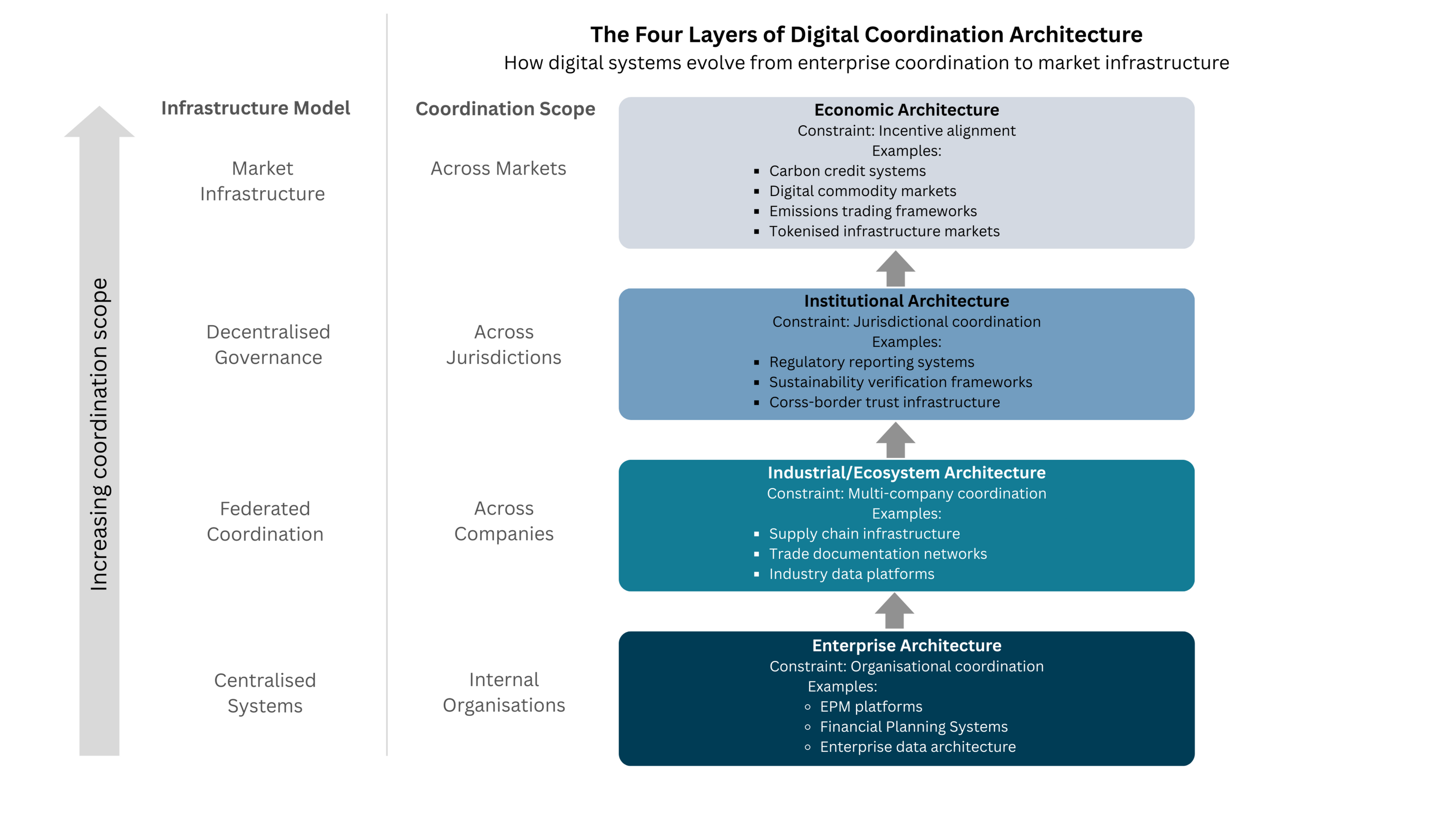
Enterprise Architecture
Coordinates activities within organisations.
Examples include enterprise planning systems, ERP/MRP, operational software, and enterprise data architecture.Industrial / Ecosystem Architecture
Coordinates activity across multiple organisations within an industry or supply chain.
Examples include supply chain infrastructure, trade documentation networks, and industry data platforms.Institutional Architecture
Coordinates governance across organisations and jurisdictions.
This layer introduces authority, policy and verification mechanisms that allow independent actors to operate under shared rules.
Examples include regulatory reporting systems, sustainability verification frameworks and cross-border trust infrastructure.Economic Architecture
Coordinates incentives and value exchange across markets.
Examples include carbon markets, digital commodity exchanges and emissions trading systems.Each layer builds on the coordination capabilities of the layer below. Industrial coordination enables transparency between organisations.Institutional infrastructure introduces governance and authority across those networks. Together these layers make it possible for market-level systems to emerge.The focus of this paper is the institutional layer of digital infrastructure, which provides the governance foundation required for reliable coordination across institutional networks.
5. Institutional Networks (The Context - Where It Applies)
Many real-world economic systems operate across networks of independent organisations.
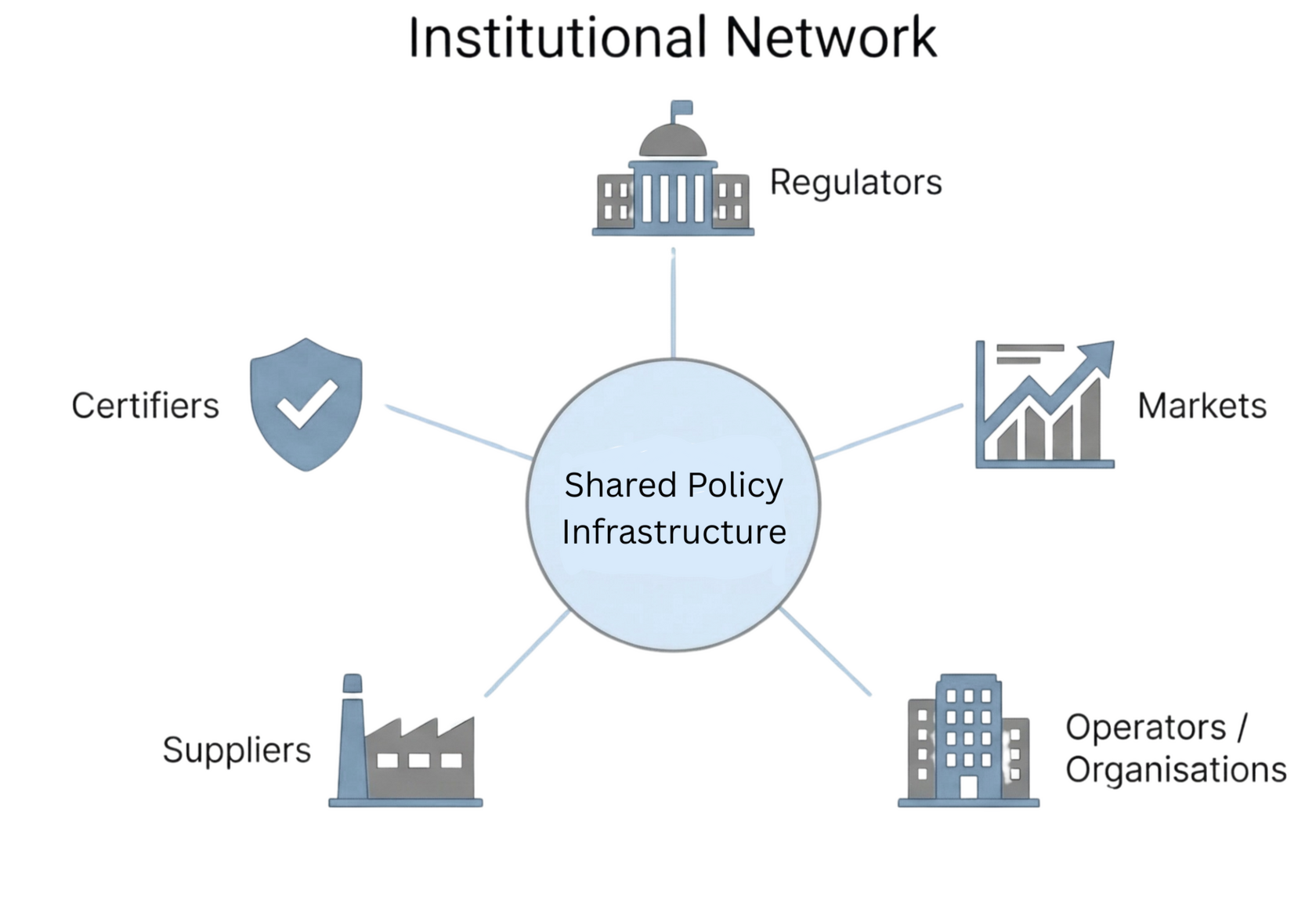
Many important economic systems operate across networks of independent organisations — including regulators, suppliers, certifiers and markets.Institutions within these networks perform defined roles that extend beyond the internal operations of any single organisation. Certain actors exercise authority, enforce shared policy, or issue attestations about activities occurring across the network.These governance roles are essential to how institutional systems function. Regulators define and enforce rules, certifiers attest to compliance, and market actors rely on these authorities when coordinating economic activity.Yet these institutional roles and authorities are rarely represented explicitly in digital systems, which are typically designed around the internal processes of a single organisation.
6. The Problem (Why Existing Thinking Fails)
Most enterprise systems (e.g SAAS/ERP) model the internal processes of a single organisation rather than the institutional roles that exist between organisations.
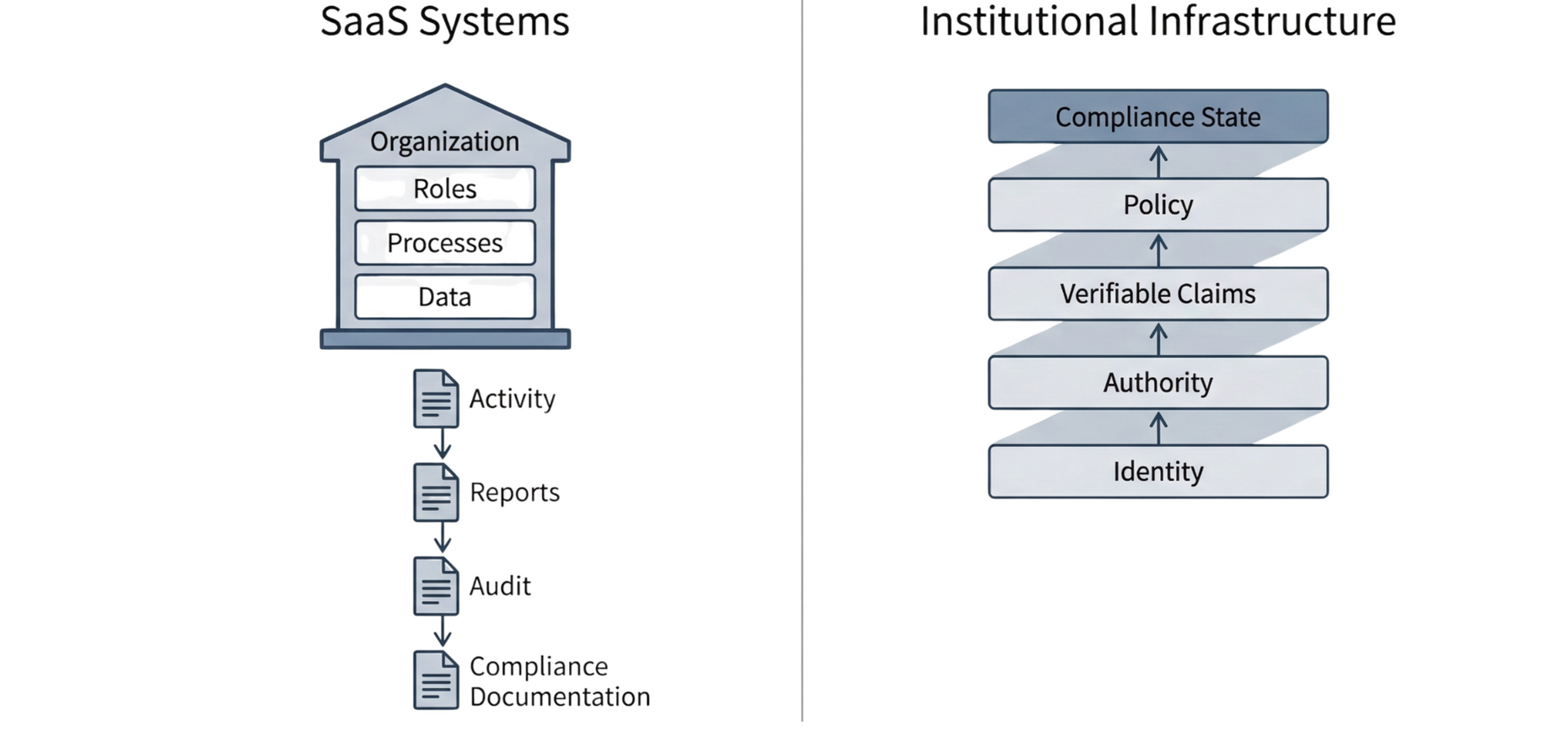
The missing layer in SAAS and digital infrastructureMost SAAS systems model the internal roles and processes of a single organisation. The broader institutional roles that exist between organisations — such as regulator, operator, certifier or supplier — are rarely represented explicitly within digital systems and are instead handled through documents, reporting and audit.What is needed is a form of digital infrastructure that embeds identity, authority and policy directly into the architecture of multi-party systems.
7. Open Standards Foundations
Practical Implementation of Architecture
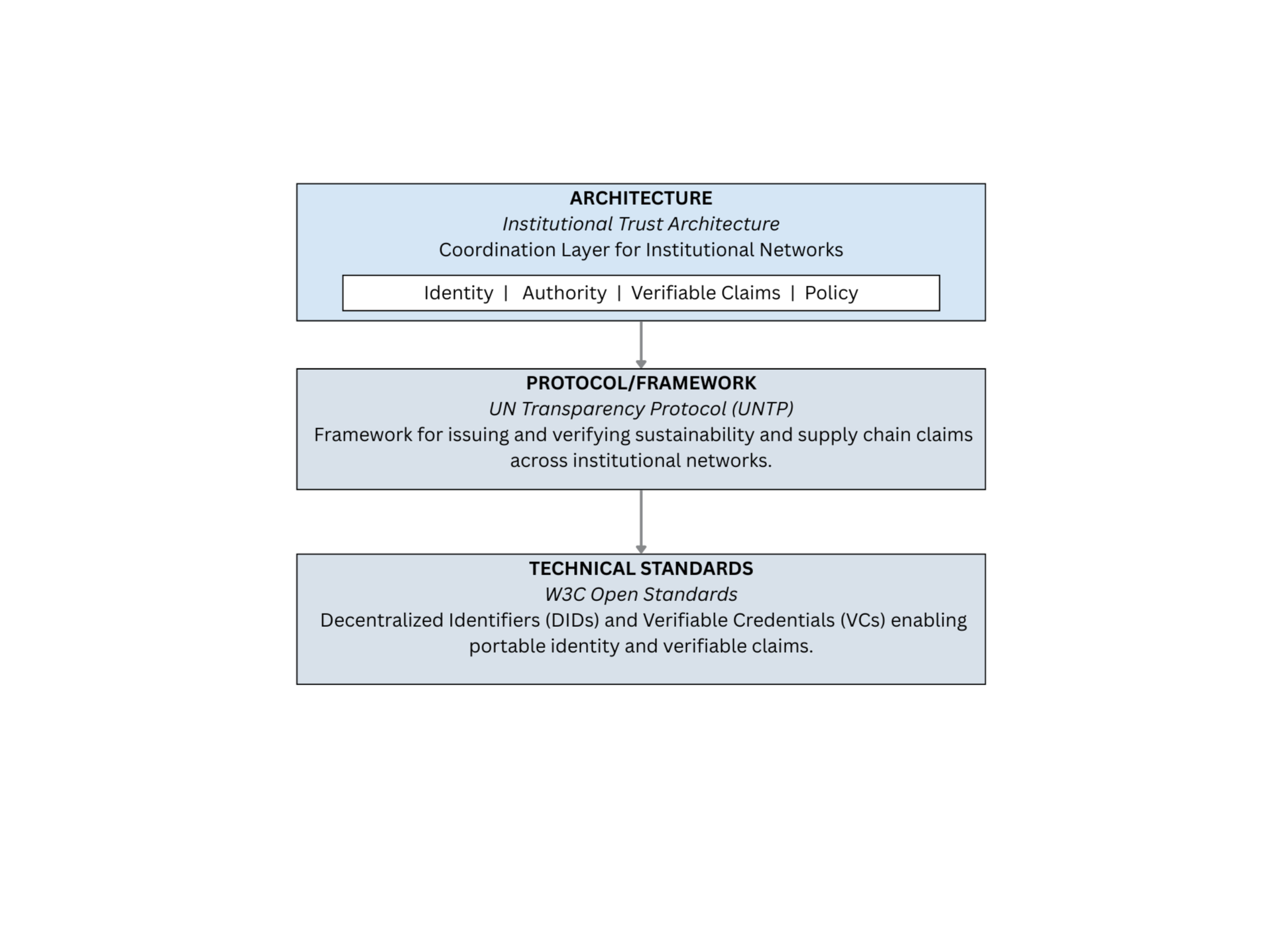
The Institutional Trust Architecture described here does not rely on proprietary platforms or vendor-specific technologies. Instead, it aligns with a growing ecosystem of open standards designed to support interoperable digital trust infrastructure across institutional networks.Open standards play an important role in institutional coordination because they allow independent organisations to exchange information, verify claims and enforce shared policy without requiring a single controlling platform. By defining common protocols and data structures, open standards enable systems developed by different organisations to interoperate reliably.This architecture draws on two key developments in open standards.At the technical layer, the World Wide Web Consortium (W3C) has defined standards such as Decentralized Identifiers (DIDs) and Verifiable Credentials (VCs). These standards provide mechanisms for portable digital identity and verifiable claims that can operate independently of individual organisational systems.Building on these foundations, the United Nations Transparency Protocol (UNTP) provides a framework for applying these capabilities within institutional networks such as sustainability reporting, supply chain transparency and regulatory compliance. UNTP defines shared approaches for issuing, exchanging and verifying claims between independent organisations.Together, these standards provide a practical pathway for implementing the institutional trust primitives described in this architecture. Rather than introducing new proprietary systems, the Institutional Trust Architecture describes how these existing standards can be used to enable coordination, verification and policy enforcement across institutional networks.The relationship between these layers is illustrated below.
8. Principles (Guiding Philosophy)
Infrastructure for institutional networks must make identity, authority, policy and verifiable information explicit.
The design of digital infrastructure for institutional networks is guided by several principles.Institutions matter
Many digital systems assume a single organisation operating in isolation.
However real-world economic systems operate across networks of independent institutions with different responsibilities, authorities, and incentives.Authority and accountability must be explicit
In regulated environments, certain actors have the authority to certify, attest, or enforce rules.
Digital infrastructure must make these authorities visible and verifiable within the system.Policy should be executable
Compliance is traditionally demonstrated after the fact through audits and reporting.
Infrastructure should instead allow policy rules to be evaluated and executed during system operation.Verifiable information builds trust
Actors in institutional networks must be able to rely on information issued by others.
Verifiable claims and attestations allow organisations to coordinate without requiring centralised control.
9. Institutional Trust Architecture (Practical Framework)
Institutional Trust Architecture defines the layers required for coordination across organisational networks.
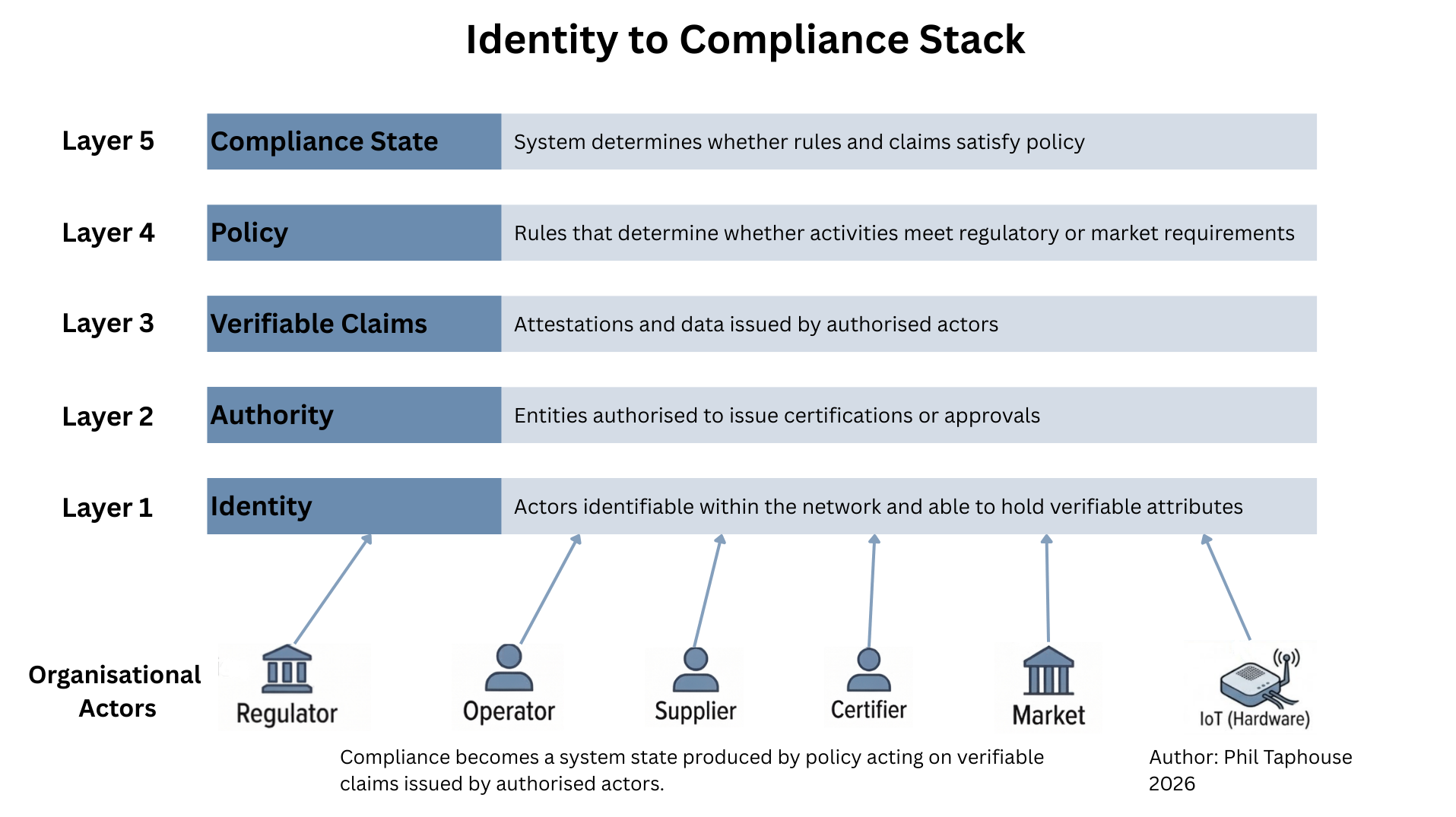
Institutional Trust Architecture describes how organisations coordinate through shared digital infrastructure rather than isolated systems.The architecture can be understood as an Identity-to-Compliance stack for institutional networks.The framework introduces a layered model where identity, authority, verifiable claims and policy interact to produce a compliance state within the system itself.Instead of reconstructing compliance through reporting and audit after the fact, the architecture allows rules to be evaluated during system operation.
Institutional coordination requires a small set of fundamental capabilities. These form the trust primitives of the architecture.
| Primitive | Role | Example |
|---|---|---|
| Identity | Defines actors in the network | Vessel, fuel supplier, regulator |
| Authority | Determines who may issue claims | Classification society |
| Verifiable Claims | Evidence about events or attributes | Fuel certificate, data |
| Policy | Determines compliance rules | IMO emissions rule |
10.Operational Example: Global Shipping Supply Chains
In complex economic systems like global shipping, trust is currently a point-to-point exercise. Suppliers, laboratories, regulators, and certification bodies exchange documents directly. This forces every participating organization to independently verify the exact same information, creating a massive, duplicated administrative overhead across the ecosystem.Institutional Trust Infrastructure replaces this spaghetti architecture with a shared validation layer.Instead of every organization independently validating the same documents, verifiable claims enter the network through a single, shared entry point: The Trust Gateway API.Think of this as the compliance equivalent of a modern payment gateway. Organizations integrate once with the network by submitting verifiable credentials (such as a Bunker Delivery Note or a fuel composition certificate) through a standard API endpoint.The Gateway automatically performs three critical checks before any information becomes part of the institutional record:1. Identity: Who is submitting the data?2. Authority: Is this actor authorized by the network to issue this specific type of claim?3. Validity: Is the credential structurally sound and cryptographically verifiable?By standardizing the entry point, the Gateway ensures that all trust data is validated consistently. Once a credential clears this gateway, it can be universally relied upon by other participants, eliminating the need for repeated, bilateral verification.
Operational Architecture of Institutional Trust Infrastructure (Bunker Delivery Note (BDN) Example)
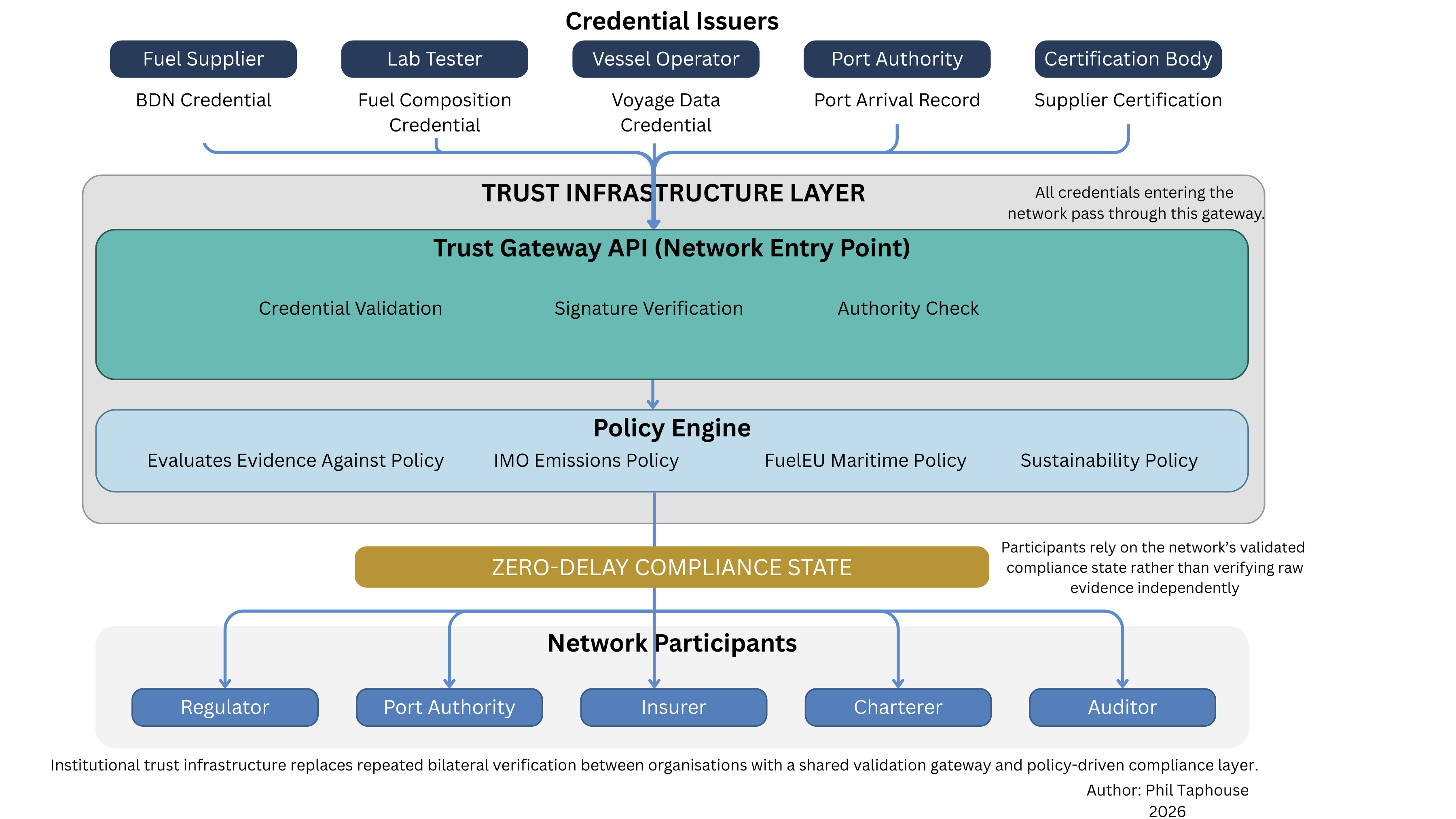
Infrastructure Rather Than IntegrationThis model represents a fundamental shift in how multi-party systems operate: moving from isolated organizational integration to shared infrastructure.Instead of building dozens of costly, bilateral IT integrations with every counterparty, participants integrate once with the Trust Gateway. Once a credential is systematically validated at this infrastructure layer, it generates a verified Compliance State.This allows downstream participants—such as port authorities, insurers, charterers, and auditors—to instantly rely on the validated compliance state rather than manually reconstructing the raw evidence from scratch.Economically, the value of this architecture scales across the network. By shifting the burden of verification from individual organizations to the shared infrastructure itself, we eliminate the duplicated effort that currently costs the global supply chain billions in administrative overhead. It is the technical foundation that makes the 25% efficiency dividend possible.
11. The Execution Path: Building the Minimum Viable Consortium (MVC)
Architecture without an execution path is just theory. A CIO or Enterprise Architect evaluating this blueprint faces a critical question: How do we build this without ripping out our core ERP instances and risking the business?They do not need another massive IT transformation project; they need a de-risked, structured methodology. They need a map through the minefield of their enterprise stack.The Institutional Trust Architecture provides this map through a targeted deployment model: the Minimum Viable Consortium (MVC). You do not need to force industry-wide adoption or rebuild your internal systems to achieve a Zero-Delay System State. You only need to connect three specific primitives in a controlled sandbox to prove the logic.To execute this safely, we isolate a single, high-friction transaction and establish the trust triad:1. The Originator (Issuer): The entity creating the verifiable truth at the source (e.g., the lab certifying a green hydrogen asset).2. The Consumer (Holder): The entity holding the asset and needing to prove its compliance (e.g., the shipping line).3. The Authority (Verifier): The digital policy engine that evaluates the claim to authorize the transaction.The De-Risked Orchestration StrategyBy isolating these three nodes, organizations can deploy the ITA framework without threatening their existing operations.
12. From Audit to Executable Policy (Real-World Implication)
Compliance shifts from retrospective reporting to a state produced directly by system infrastructure.
Traditional compliance and regulatory reporting are often performed retrospectively. Organisations gather records from multiple systems and counterparties in order to demonstrate that rules were followed.However, as markets accelerate and Agentic AI enters the supply chain, this retrospective model breaks down. You cannot govern a machine-speed agent with a human-speed audit. Autonomous systems require an Execution Boundary—real-time governance that dictates what can happen at the exact moment of action.Because an Institutional Trust Architecture embeds verifiable claims into the transaction flow, policy and compliance are executed in real-time.When an institution—or an autonomous AI agent—interacts with the network, it does not just send data; it submits a verifiable claim. A Trust Gateway evaluates that claim against a digital policy defined by the governing authority.If the claim meets the policy, the transaction is authorised and a compliance record is generated simultaneously. This moves the system from retrospective audit to real-time, executable policy—creating a zero-delay compliance state that makes autonomous execution both possible and secure.
13. Where This Architecture Applies
This architecture applies anywhere independent organisations must coordinate under shared rules.
Shipping and fuel provenance
Tracking the origin, certification, and compliance status of fuels across producers, suppliers, ports, and regulators.Energy supply chains
Verifying production methods and sustainability attributes across hydrogen, biofuels, or electricity markets.Supply chain transparency
Capturing claims and certifications issued by authorised entities across complex production networks.Regulated financial systems
Embedding identity, compliance checks, and policy enforcement within transaction infrastructure.These examples illustrate how institutional architecture can support networks that must operate under regulatory and governance constraints.
14. Common Questions
Why now?Several developments are converging.Regulatory frameworks increasingly require verifiable information across organisational boundaries, particularly in areas such as supply chains, emissions reporting, and financial compliance.At the same time, digital identity and verifiable credential technologies make it possible to represent actors, authorities, and attestations directly in digital systems.These developments make it feasible to build infrastructure that supports institutional coordination rather than relying solely on internal organisational systems.If this approach is valuable, why isn’t everyone already doing it?Most digital systems are built and funded by individual organisations.Infrastructure for institutional networks requires coordination between multiple parties, shared governance models, and agreement on roles and authorities.As a result, these systems tend to emerge more slowly, often through industry collaboration, standards bodies, or regulatory initiatives.Many forms of shared infrastructure — including financial clearing systems and internet standards — evolved in a similar way.What changes if this architecture is adopted?The most important shift is that compliance and coordination can become part of the system’s operation.Instead of reconstructing compliance through reporting and audit after activities occur, policy rules can be evaluated during system operation using verifiable claims issued by authorised actors.This allows compliance to be treated as a system state rather than a retrospective reconstruction.Isn’t what we have today already working?In many cases existing systems do work, but they rely heavily on reconciliation, reporting, and manual verification between organisations.As regulatory and market complexity increases, these approaches become slower, more expensive, and harder to verify.Embedding identity, authority, verifiable claims, and policy into infrastructure allows these systems to operate more efficiently and with greater transparency.
15. Advisory
I work with organisations exploring digital infrastructure for systems that operate across multiple institutions.This includes:• Ecosystem and network architecture
• Governance and trust frameworks
• Digital identity and verifiable credential systems
• Policy-aware digital infrastructure
• Strategic exploration of Web3 and decentralised technologies in regulated industriesMy work typically focuses on early-stage architecture, strategic design, and translating regulatory or policy requirements into technical frameworks.
15. Contact
If you are exploring the architecture of multi-party systems, digital identity infrastructure, or verifiable data exchange across institutional networks, feel free to reach out.Author
Phil Taphouse
Melbourne, Australia
Institutional digital infrastructure and ecosystem architecture.©️ 2026 Phil Taphouse
© 2026 Phil Taphouse | Institutional Trust Architecture Model.